Infinite Key Multiple Time-Variant Formation Point Theory The Possibility of the World's Strongest Security "X views (impressions) exceeded 260,000 within one day of media release. (X has been viewed more than 260,000 times in the first day of its media release. Next-generation, PIN-free security, an evolution of Zero Trust Cutting-edge security
~Disclosing the critical difference between Zero Trust and Zero Trust: about after logging in.
株式会社ポイント機構
The Point Organization, Inc. is pleased to announce that X posts related to the media release "The Possibility of the World's Strongest Security, An Evolution of Zero Trust, The Next Generation of Cutting-Edge Security without the Need for PINs," published on March 24, 2026 with K Trust Corporation, recorded 261,000 views in the first 24 hours after publication. X impressions in one day.

X impressions exceeded 260,000 in one day
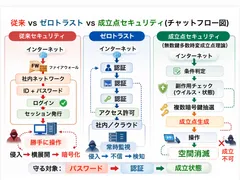
Comparison of chat flow with the previous version
X
Possibility of the World's Strongest Security from Japan Theory of Multiple Time-Variant Number of Keys that Eliminates the Need to Memorize and Input PINs, IDs, etc.
X Link
https://x.com/Press__official/status/2036246629569773586?s=20
Description
https://share.google/gSR48ltOZAzjLyiAW
YouTube video explanation list
[About Zero Trust vs. Establishment Point Security
https://youtu.be/rOjugXCmKz0?si=nRVailF1Wmx3E0LL
About the contents after logging in with Formation Point Security]
https://youtu.be/ba-lk05dABo?si=CS8uEJujQxfHg6Y6
About the contents of the login]
https://youtu.be/W09Wwy6bEVU?si=tBhqtHaB8Mmoif4-
[About eliminating the need for a PIN or ID]
https://youtu.be/IkQZSjOUpOQ?si=nH2jdQcj4sDVJ562
[Regarding multiple combined patent rights]
https://youtu.be/hxV3rdUfklY?si=Wf-Q675fr-tTfnjM
■ Summary of Presentation
This submission transmits a new security theory "Infinite-Key Multiple-Time-Variant Formation Point Theory," which has generated a high level of interest in next-generation security. Yuki Takeuchi of Point Organization, Inc. and K Trust Corporation have published a new security theory, "Myriad Key Multiple Time-Variant Establishment Point Theory" security. This theory is positioned as a next-generation state-of-the-art security structure that goes beyond conventional and zero-trust, and is a multiple layer of defense against viruses in the system,
No password is required.
No fixed keys
Automatic virus checks on multiple layers
Instantaneous control of the status of establishment.
This is a new security concept characterized by the following features
Limitations of Conventional Security
Conventional security is
Fixed IDs
Fixed passwords
Fixed passwords ● Fixed keys
Fixed passwords ● Fixed keys ● Fixed session continuity
The structure of conventional security is as follows Therefore, it is possible for a user to
Once the authentication is breached, it can be deployed horizontally.
Encryption can be performed after authentication
AI has the advantage of trial
AI has the advantage of trial by trial.
Positioning of Zero Trust
Zero Trust is based on the concept of "trusting no one.
Always authenticated
Continuous monitoring
Continuous monitoring. However, in essence, since there is a fixed correct answer (ID/token),
Attacks after authentication is breached
lateral expansion
Abuse of execution rights
However, the new theory is not a perfect solution.
New Theory
Establishment point security → This theory is fundamentally different from the conventional one.
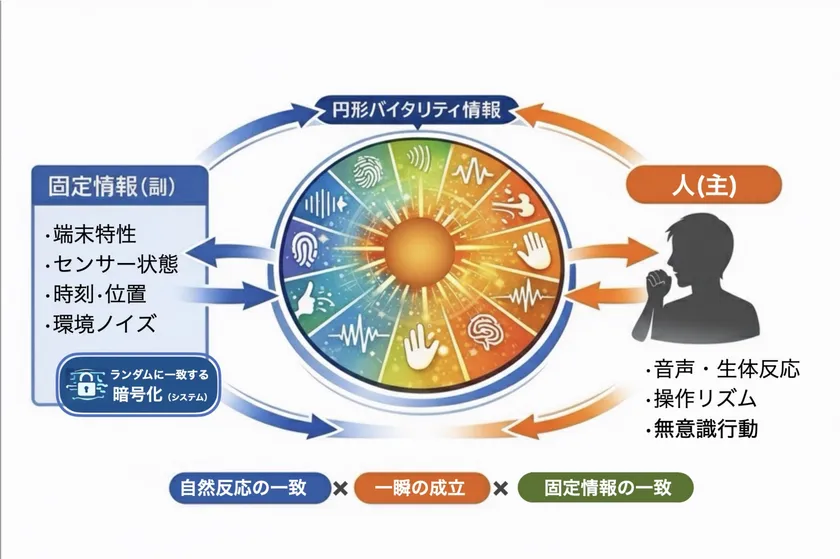
The core of this theory is that "formation itself is limited to a single moment.
Formation space model
Normal: Does not exist
Conditional matching: Instantaneous generation
After operation: Instantaneous disappearance
In case of an anomaly: Immediate interruption
In other words, formation is a "time event" and cannot be reused.
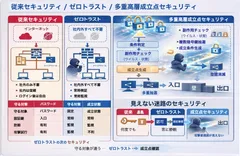
Multi-Layered High-Level Structure (L1-L5) → This theory is controlled by a 5-layered structure.
L1: Entrance (login) → Check user, terminal, and environment
L2: Side effect check → virus and abnormal behavior detection
L3: Key draw → random generation of multiple encryption keys each time
L4:Status of establishment→Only when conditions match, permission is granted for a moment
L5:Disappearance of space→Disappearance of passage after operation is completed
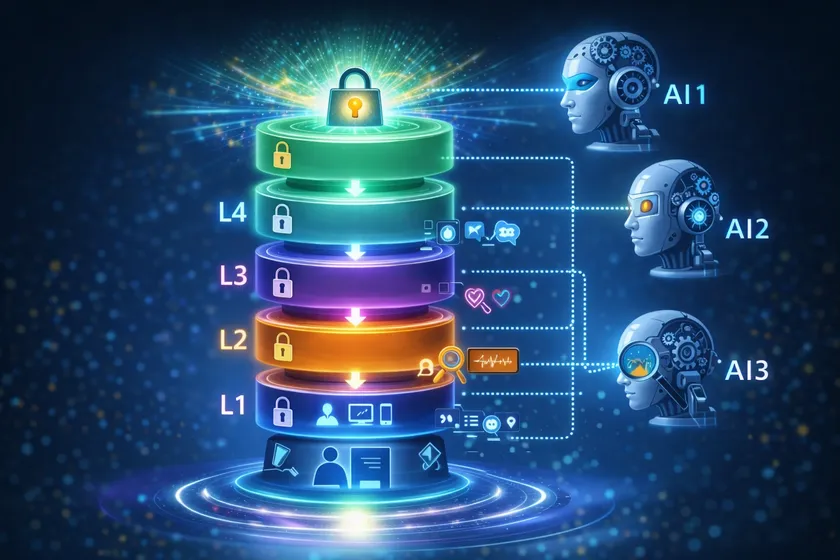
Enhanced by Multiple High Layers and Triple AI
The biggest features
(1) Key is not fixed: encryption keys are
Temporary
Random
Random ● Multi-layer generation
Random ● Non-reusable
All checks are secure.
In other words, the structure has no fixed ciphers.
(2) Multi-layered automatic virus check: At each layer
Behavior verification
Operation validation
Authorization abuse validation
● Operation validity verification ● Authorization abuse verification If an abnormality is detected, the key for the next tier is not issued → Operation is not validated
(3) Structure that does not issue execution rights until the end
Conventional → Operation is possible after successful login
This theory → Execution is not possible without passing through to the final layer
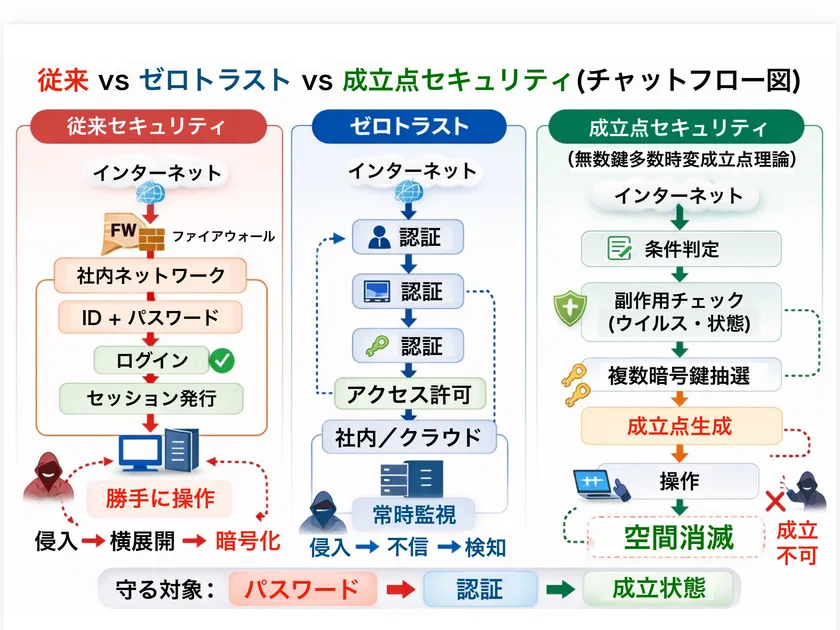
Difference from attack model
Conventional
Penetration → Breakthrough of authentication → Horizontal expansion → Encryption
This theory
Penetration → L1 passage → Side-effect check → L2 key → Side-effect check → L3 key → Fulfillment point → Execution
Abnormality detection during execution → Immediate blocking
Effect on ransomware
Ransomware requires the right to execute encryption
In this theory
Control by privileged key (L3)
Blocked by side-effect detection
Space extinction and cannot be reused.
As a result, encryption is difficult to be established.
Numerical model (design value): ransomware
Conventional defense ratio: approx. 55.9
This theory: 99.7% or higher
● Damage probability: approx. 0.3% or less
Improvement factor: Approx. 176 times
Comparison of 73 attacks
Phishing
AI fraud
Malware
API abuse
Cross-platform
The theory has been proven to significantly improve the effectiveness of 73 types of attacks, including
Technical essence: This theory
No fixed secret
Establishment is a time event
The number of attempts is not advantageous.
The more the attacker tries, the less favorable the result.
This is a physics-based formation control model.
In a nutshell
Conventional → Protect the correct answer
Zero Trust → Do not trust
This theory → do not allow it to be established
Conclusion
The theory of infinite-key multiple time-varying fixed points is
Next generation of Zero Trust
No password required
No password required
Multilayer, high-layer security
Instantaneous control of execution rights
This is a next-generation, state-of-the-art security infrastructure that realizes
This technology is a new security theory that structurally prevents conventional "damage after authentication breakthrough" by not fixing encryption keys and allowing operations to be executed only when security is confirmed through automatic virus checks using a multi-high-layer structure.
About Point Organization, Inc.

The Point Organization, Inc.
Company name: Point Organization, Inc.
Representative: Yuki Takeuchi, Representative Director
Head office: Room 301, HOUSE 2717, 2-7-9 Sendagaya, Shibuya-ku, Tokyo
Date of establishment: December 24, 2021
Fiscal year end: March
URL : https://point-kikou.co.jp/
Official website (edinet) URL for the FSA Supervisory Public Search:
https://disclosure2.edinet-fsa.go.jp/WEEE0030.aspx?bXVsPeODneOCpOODs+ODiOapn+aniyZjdGY9b24mZmxzPW9uJmxwcj1vbiZycHI9b24mb3RoPW9 uJnBmcz03Jnllcj0mbW9uPQ==
■About K Trust Co.

K Trust
Company Name : K Trust Co.
Representative : Tomoko Hirakawa and Kazunori Hirakawa, Representative Directors
Headquarters : 1-3313 Shimoshidami, Moriyama-ku, Nagoya-shi, Aichi, Japan
URL : https://www.ktrust.info
Relationship with Point Organization: Sole agent for A-GEL gift points & A-GEL gift cards
- Category:
- Corporate Trends
- Genres:
- Technology General Business Economy(Japan)