Presentation of the Fundamentals of Strongest Security Theory Security, including ransomware and server attacks evolve to the strongest possible level through API connections without infrastructure changes.
Why Do Cyber Attacks Repeat "Learning"? New Security Theories Show Structural Problems
株式会社ポイント機構
Cyber attacks targeting businesses and local governments are becoming more sophisticated every year. Behind this is a structure in which attacks are repeatedly tried and learned.
(Head office: Shibuya-ku, Tokyo; CEO: Yuki Takeuchi; hereafter, "Point Organization"), which operates the point redemption system "A-GEL Gift Point," and K-Trust Co. (headquartered in Moriyama-ku, Nagoya, Aichi Prefecture; Tomoko Hirakawa and Kazunori Hirakawa, CEOs; hereinafter referred to as "K Trust") have applied for a patent for a new theory "infinite key multiple time-varying fixed point theory," which reviews this structure itself. Some of the patents have already been granted.
In this newsletter, we explain the weaknesses of conventional security methods and the differences between the new design philosophy.

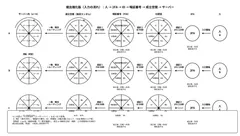
Overall Diagram of the Strongest Security Theory
In the circle in the upper center on the right of the above image, biometric and motion authentication information, etc., are registered in advance to form a cryptographic key for each of them, which are then rotated by roulette.
The first explanatory video you will see is
▼ The basic of the theory of infinite key multiple time-varying configuration points.
▼ Explanatory video on some of the patented multiple compound patent rights
https://youtu.be/hxV3rdUfklY?si=cvV4BIYRDmiFwaAT
Conventional security has a "fixed correct answer
Many current systems are,
IDs
Passwords
Sessions
Sessions ● Permissions
Many current systems are designed with the assumption of "fixed correct answers" such as ● ID ● Password ● Session ● Permissions.
In this structure, an attacker can gain information by increasing the number of attempts.
In other words, the attacker becomes stronger with experience.
From "secret" to "state" as the object to be protected by security
In the new theory, the object to be protected is not a secret (e.g., passwords) but the state of the system itself.
The state of existence is
The state is generated only at the moment when the conditions are met.
Disappears after a certain period of time
Cannot be reused
The new theory is based on the following mechanism.
Access is managed in 5 states
In theory, the access states are
Disabled
Enabled
Continued
Revoked
Revoked
The five states are "invalid," "valid," "continued," "expired," and "blocked.
Normally, the state is "invalid", and the establishment is treated as an exceptional state for a very short period of time.
The design model has a high protection ratio, but the theoretical model in the document is as follows
Protection rate of 99% or higher
Damage probability less than 0.3%.
The design KPI is also shown as a theoretical model.
However, these are not empirical values but theoretical design values.
An attempt to demonstrate a change in security philosophy
The theory of this time is as follows
Enhanced Authentication
Enhanced monitoring
Unlike conventional "patch-and-add" countermeasures, such as ● strengthening authentication ● strengthening surveillance, the new theory takes the approach of redesigning the system structure itself. As cyber attacks become more sophisticated due to AI, this theory may attract attention as a new direction for security design.
About Point Organization, Inc.
Company name: Point Organization, Inc.
Representative: Yuki Takeuchi, Representative Director
Head office: Room 301, HOUSE 2717, 2-7-9 Sendagaya, Shibuya-ku, Tokyo
Date of establishment: December 24, 2021
Fiscal year end: March
URL : https://point-kikou.co.jp/
Official website of FSA Supervisory Public Search (Edinet) URL: https://disclosure2.edinet-fsa.go.jp/WEEE0030.aspx?bXVsPeODneOCpOODs+ODiOapn+aniyZjdGY9b24mZmxzPW9 uJmxwcj1vbiZycHI9b24mb3RoPW9uJnBmcz03Jnllcj0mbW9uPQ==
About K Trust Co.
Company name: K Trust Co.
Representative: Tomoko Hirakawa and Kazunori Hirakawa, Representative Directors
Headquarters : 1-3313 Shimo-Shidami, Moriyama-ku, Nagoya City, Aichi Prefecture, Japan
URL : https://www.ktrust.info
Relationship with Point Organization: Sole agent for A-GEL gift points & A-GEL gift cards
- Category:
- Corporate Trends
- Genres:
- Technology General Business Economy(Japan)